How to Detect a Rogue Device the Instant It Connects to your Network

Hackers are ruthless in their persistence and fortitude. It can take weeks or months for them to gather intelligence on your IT vulnerabilities, penetrate your network, and exfiltrate your precious data. But they know, and statistics prove this, that, for the most part, their victims have no idea that their network infrastructure is under attack – until it’s too late.
As we pointed out in this article – Getting to Know the “Enemy with No Face” is Critical to Winning the Cyber War – it took approximately 17 months for the Office of Personnel Management to detect the now infamous breach of 2015.
Detection is a big problem, especially in complex enterprises where the IT footprint gets larger and larger.
But what if you could discover a rogue device the instant it connects to the network, block it instantly, and remediate any potential damage caused – even in large and dynamic environments?
Consider an Agentless Approach to Endpoint Visibility and Control
DLT partner, ForeScout Technologies has pioneered an agentless approach to network security that effectively helps address the challenges of endpoint visibility and control across servers, desktops, smartphones, IoT devices, peripherals, network infrastructure components and rogue devices the instant they connect to the network – even if they don’t have security agents installed.
You can take control and stamp out any malicious activity before it has a chance to propagate.
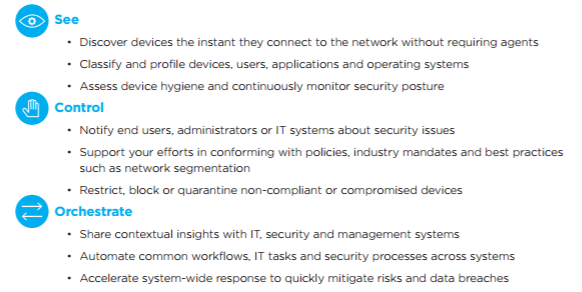
Once the ForeScout CounterACT® platform discovers a security problem on a device, its sophisticated policy manager can automatically execute a range of responses depending on the severity of the problem. Minor violations might result in a warning message sent to the end user. Employees and contractors who bring their own devices can be redirected to an automated onboarding portal. Serious violations could result in actions such as blocking or quarantining the device, reinstallation of a security agent, re-starting of an agent (such as third-party antivirus software) or process, triggering the endpoint to retrieve an operating system patch, segmenting to a more secure VLAN, or performing other remediation actions.
Tear Down Security Silos
Then you can orchestrate your response. CounterACT includes an optional module that lets you orchestrate information sharing and policy-based security enforcement between CounterACT and leading IT security management products.
Why is this necessary?
Today’s security infrastructures are complicated beasts. They rely on point solutions which operate in independent silos – a disjointed approach that prevents a coordinated, enterprise-wide security response, giving hackers more time to exploit vulnerabilities. It also depends on manual processes that aren’t scalable.
Instead, ForeScout orchestrates system-wide security management to make formerly disjointed security products work as one. This unique set of network, security and management interoperability technologies extends the power of CounterACT to more than 70 third-party solutions, allowing the combined system to accelerate response, achieve major operational efficiencies and provide superior security. So you can share contextual insight, automate workflows and response actions.
The ForeScout platform includes a range of capabilities that fall into three categories:
Check out this whitepaper to learn more about agentless visibility, control and security orchestration.