Safeguarding and Monitoring Your Agency’s IT Environment

By Mav Turner, VP, Product Management, SolarWinds
For federal IT pros, moving to a cloud environment is a “when” rather than an “if” proposition. From the government’s recently released Report on IT Modernization, calling for agencies to identify solutions to current barriers regarding agency cloud adoption, to the White House’s draft release of a new “Cloud Smart” policy, which updates the “Cloud First” policy introduced in 2010; cloud migration continues to be a priority.
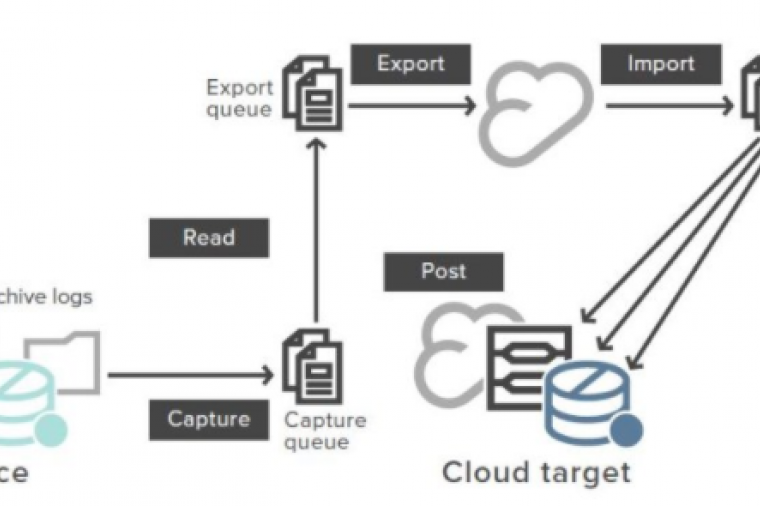
Whether you’re moving everything to the cloud or choosing a hybrid cloud option, moving to this environment brings several well-documented advantages, such as flexibility, the potential for innovation, and cost savings. Yet it is critically important—and I cannot state this strongly enough—to maintain a secure cloud environment.
This may seem overwhelming, particularly when there is a wide range of data that falls under an equally wide array of privacy, policy, and security regulations. Data moving across these hybrid environments requires monitoring solutions that span the entire distributed network and adapts as network environments change.
So, what steps can you take to make your cloud environment more secure? While there are countless options, the three most critical steps are:
• Create and enforce management policies
• Enhance visibility
• Implement automation
The good news is technology is advancing quickly enough that you can likely find a series of tools, or even a single toolset, that will go a long way toward accomplishing all three of these with minimal interruption and maximum advantage.
Create management policies
Compliance is second nature to federal IT pros; creating and enforcing management policies to maintain control within a hybrid cloud environment is a simple next step to compliance that you may already be accomplishing.
“Management policies” can mean a lot of things. For cloud security, I’m referring to configuration management, transaction management, and activity monitoring. Specifically, be sure you’re using a solid network configuration tool to deploy standardized configurations, detect out-of-process changes, audit configurations, and even correct violations. Be sure you can back up those standardized configurations in case something goes wrong and you need to roll back to a previous iteration.
There’s a good chance you’re already doing these things. The key to bolstering security across a hybrid cloud environment, in particular, is to be able to integrate this with the next two steps.
Enhance visibility
The ability to see devices and activity across multiple connected environments is a must for security. Look specifically for the ability to implement a control-room view of sorts—something that allows you to collect and act on performance data from any part of the cloud, from remote locations, and even from networks managed by different groups within the agency. Make sure you can do this in real time; the more you can see, the more you can control effectively.
Implement automation
The larger and more disparate the cloud environment, the harder it will be to manage the network; which is why having an automated system is key.
Start by automating your discovery process. Be sure you can automatically detect new devices and any other changes to network topology. Automate monitoring and alerting across the entire environment. Next, correlate the results of that effort; the larger the environment, the more data you’ll be grappling with. Automating will not only save you time, it will also dramatically reduce the impact of human error.
Conclusion
As networks grow and become more complex—particularly in the case of hybrid cloud environments—they become harder to secure. There are no silver bullets. That said, creating management policies, enhancing visibility, and implementing automation will certainly go a long way toward providing more effective monitoring and shoring up security; even as the network grows.