TD SYNNEX Public Sector, through DLT Solutions, delivers a secure, stateside supply chain purpose-built for U.S. government and regulated public sector environments. Our approach is designed to protect the integrity of technology — from sourcing through fulfillment and lifecycle support — while meeting the operational, compliance and risk expectations of public sector organizations.
CMMC L2 Certified
TD SYNNEX Public Sector has achieved Cybersecurity Maturity Model Certification (CMMC) L2, validating our ability to protect Controlled Unclassified Information (CUI) and meet the Department of Defense’s stringent cybersecurity requirements for the Defense Industrial Base.
CUI Ready
DLT can process Controlled Unclassified Information (CUI) marked purchase orders today. Our security-aligned operations enable partners and vendors to pursue and support CUI-sensitive opportunities without disruption or compliance friction.

Designed for Government and Regulated Environments
Our operational model is architected to provide confidence and control throughout the technology acquisition lifecycle. Key pillars of our approach include:
 | U.S.-Based Operations Core processing, support, and data handling are performed in the United States, supporting government expectations around control, accountability, and oversight. |  | Compliance-Aware Execution Our processes align to federal acquisition requirements and recognized security frameworks, supporting sensitive and controlled technology buys. |
 | Verified Product Integrity Controls are in place to help ensure authenticity, traceability, and accountability throughout the procurement and fulfillment process. |  | Lifecycle Accountability Beyond delivery, we support renewals, entitlement management, and ongoing operational hygiene to reduce long-term risk. |
Inquiries
If you have questions about our secure supply chain or how our capabilities align with your mission or program requirements, please contact us at: SecureSupplyChain@dlt.com.
CMMC L2 Certification: Validated Cybersecurity for the Defense Industrial Base
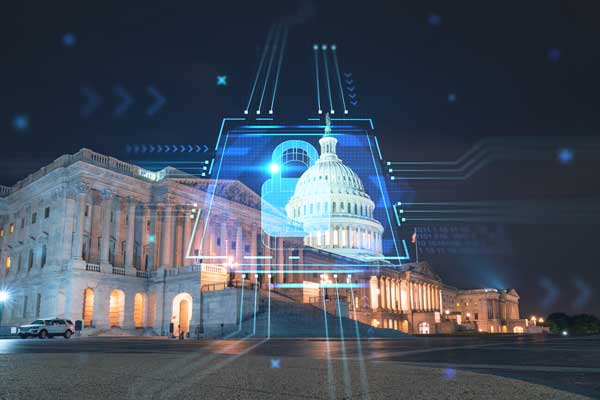 DLT has achieved CMMC L2 certification, reflecting the maturity of our security controls, operational discipline and long-standing commitment to safeguarding sensitive data across the public sector ecosystem. This certification is a formal validation of our ability to protect CUI and meet the Department of Defense’s cybersecurity requirements.
DLT has achieved CMMC L2 certification, reflecting the maturity of our security controls, operational discipline and long-standing commitment to safeguarding sensitive data across the public sector ecosystem. This certification is a formal validation of our ability to protect CUI and meet the Department of Defense’s cybersecurity requirements.
Our certification provides tangible benefits to technology partners and public sector end-users:
- Reduced Risk: Engage with confidence knowing CUI is handled within a certified, compliant environment.
- Simplified Procurement: Remove uncertainty and friction — leave compliance and requirements to us.
- Supply Chain Confidence: Procure with trust, end-to-end from OEM to end-user.
Built Into How We Operate
CMMC L2 certification is not a checkbox: it’s embedded into our day-to-day operations. This foundation supports secure collaboration across defense, civilian, and adjacent public sector missions through:
 | Security controls aligned to DoD requirements. |  | Documented processes and clear lines of accountability. |
 | Ongoing monitoring and a commitment to continuous improvement. |  | Governance designed to scale with public sector partner and end-user needs. |
Inquiries
If you have questions about CMMC support or how our capabilities align with your mission or program requirements, please contact us at: SecureSupplyChain@dlt.com.
CUI Handling: Secure and Compliant Support for Sensitive Missions
DLT provides a secure and compliant environment to support programs and transactions involving CUI. With deep public sector expertise and security-aligned operations, we help partners and end-users move forward confidently when CUI is part of the mission — without delays, workarounds, or uncertainty.
Public sector partners and end-users can expect:
 | Secure, Government-Aligned Operations: Processes designed to support CUI handling across procurement, contracting, and fulfillment. |  | Public Sector Expertise: Decades of experience supporting defense and civilian agencies with compliance-aware supply chain operations. |
 | Reduced Friction: Fewer delays related to data handling requirements, contract language, or compliance readiness. |  | Confidence to Engage: A trusted environment for partners and vendors supporting CUI-sensitive missions. |
A Commitment to Continuous Improvement
Security and supply chain integrity are not static. In addition to supporting CUI today, DLT Solutions continues to evolve its cybersecurity posture to align with emerging federal requirements and industry standards. This ongoing commitment helps ensure partners and customers are supported by a supply chain built for today and ready for what comes next.
Inquiries
If you have questions about CUI support or how our capabilities align with your mission or program requirements, please contact us at: SecureSupplyChain@dlt.com.