Key Findings of 2018 Cyber Threat Report and How Government Can Respond

Symantec’s 2018 Internet Security Threat Report is here. Based on data collected by Symantec’s massive security infrastructure (the largest civilian threat collection network in the world), the report has become the de facto standard for giving enterprises and public organizations essential information to help secure their systems effectively.
By the nature of the topic, the report isn’t an easy read. Expect to be perturbed. However, the insights provided into today’s rapidly evolving threat landscape are invaluable.
For the year in review, 2017, the findings are hardly surprising: attackers are working harder to discover new avenues of attack and cover their tracks while doing so. But new patterns and tactics, techniques, and procedure (TTPs) are emerging, that agencies need to have on their radar.
Here are key takeaways for the public sector:
Ransomware Became a Commodity
In 2016, ransomware profitability and overpriced ransom demands led to a crowded market. In 2017, the ransomware “market” made a correction. Yes, we heard more about ransomware, think WannaCry and Petya/NotPetya, but Symantec noted fewer ransomware families and lower ransom demands. In conclusion, ransomware has become a commodity. That’s not to say that attacks aren’t declining, in fact, they are gathering pace. Symantec detected 5.4B WannaCry attacks as blocked and saw a 46 percent increase in ransomware variants last year.
Ransomware is also no longer the preserve of the cybercriminal. Targeted attack groups are taking an interest too. WannaCry, which seemed to have the hallmarks of a cybercrime operation, soon exhibited characteristics of a targeted attack group. Symantec has strong evidence that the Lazarus group, linked by the FBI to North Korea, was behind it. Targeted attack groups often use ransomware as a decoy as a cover for a potentially more disruptive intrusion-based attack. They can also use it to shore up revenue for cash-strapped regimes.
The Bottom Line: Ransomware continues to be one of the main online threats faced by organizations and consumers. Learn how you can better protect your agency.
Coinmining Attacks Explode
With the commoditization of ransomware, many cyber criminals have shifted their focus to coin mining. With the rise in cryptocurrency values, the coin mining “gold rush” has seen an 8,500 percent increase in detections of coinminers on endpoint computers in 2017.
What is coinmining?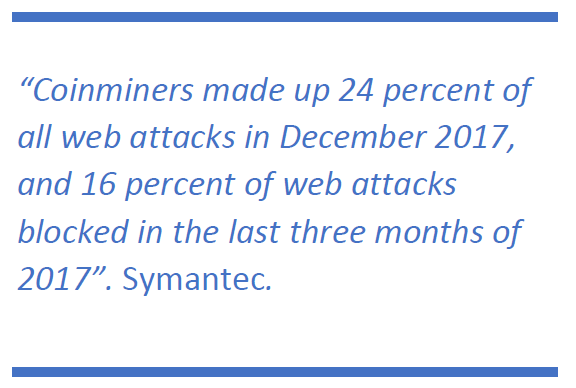
To quote Symantec: “With a low barrier of entry—only requiring a couple lines of code to operate—cyber criminals are using coin miners to steal computer processing power and cloud CPU usage from consumers and enterprises to mine cryptocurrency. While the immediate impact of coin mining is typically performance related—slowing down devices, overheating batteries and in some cases, rendering devices unusable—there are broader implications, particularly for organizations. Corporate networks are at risk of shutdown from coinminers aggressively propagated across their environment. There may also be financial implications for organizations who find themselves billed for cloud CPU usage by coinminers.”
IoT devices are ripe for attack by coin miners.
The Bottom Line: Coinmining isn’t yet illegal, to better protect your agency, review the benefits of Symantec Endpoint Protection which provides coinminer protection and removal.
Mobile Malware Continues to Surge
The number of new mobile malware variants increased by 54 percent in 2017, as compared to 2016. And last year, there were an average of 24,000 malicious mobile applications blocked each day.
Many users continue to make life easy for attackers by continuing to use older operating systems. In particular, on Android, only 20 percent of devices are running the newest major version.
The Bottom Line: While ensuring Android systems are up-to-date can help, agencies should also consider investing in advanced threat protection for mobile devices, such as Symantec Mobile Security.
Learn More
For more trends and attack methods to watch out for, download the full Symantec 2018 Internet Security Threat Report and join Kevin Haley, Director of Security Response at Symantec as he explains the latest threats in this free webinar on Thursday, April 12, 2018.