Checkmarx for Public Sector
Checkmarx provides Public Sector organizations with a comprehensive platform that allows protection of applications early, quickly, and cost-efficiently. Enabling Federal, State and Local Governments to effectively meet compliance regulations and embed security throughout the software development lifecycle to deliver and prevent security breaches. Checkmarx helps optimize Public Sector DevSecOps programs. Learn more at www.checkmarx.com/public-sector.
Federal-Grade Application Security Testing
Checkmarx’s software security testing platform is unique in the public sector. No other federal-grade platform addresses core issues with a single easy-to-deploy-and-use solution.
Federal Compliance Mandates
Checkmarx's automated approach shifts more of your security effort to the left – driving down costs and accelerating time to market. Even better, it also simplifies your ability to document security compliance.
Our easy-to-follow test reports show where your application isn’t meeting a specific standard. Your post-fix report positively documents your compliance.
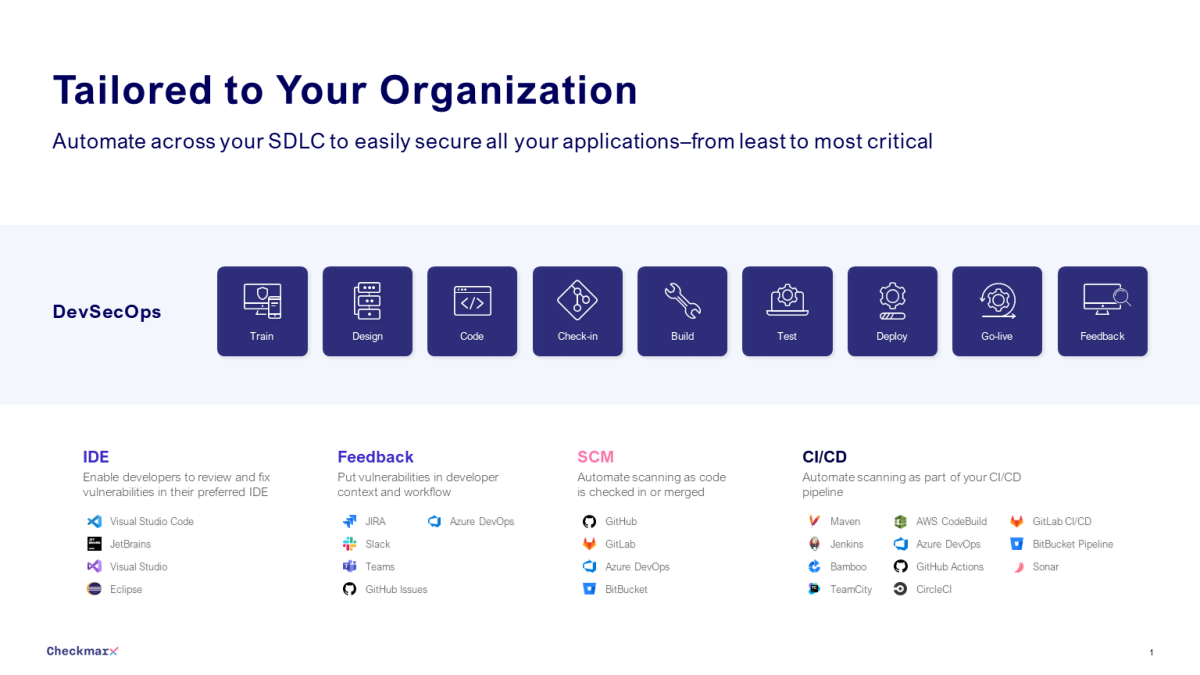
Integrate Security Testing
Checkmarx's platform has two key features that make it easier for agencies and contractors of all sizes to achieve the benefits of DevOps:
- Scan Your Source Code: Our solution lets you automatically test code at the earliest possible development point, so you can find and fix security issues, and avoid unnecessary development efforts.
- Save Precious Remediation Time: Our "Best Fix Location" feature shows you how to solve issues with the fewest changes, so you can reduce the number of test cycles required to get your code compliant.
The result is a faster path to DevOps, with just a few changes to your test process.
Train Developers to Code Securely
Codebashing helps developers learn and sharpen application security skills in the most efficient way because it is in-context and available on-demand. Codebashing is fully integrated into the CxSAST user interface so when developers encounter a security vulnerability they can immediately activate the appropriate learning session, quickly run through the hands-on training, and get straight back to work equipped with the new knowledge to resolve the problem.
Checkmarx. Make Shift Happen.
How to Fight Threats to the Software Supply Chain
On-Demand — The evolving cyber threats faced by federal agencies prompted the White House to issue Executive Order 14028 in May 2021, emphasizing the adoption of zero trust architecture by 2024. Zero trust involves continuous verification of users, devices, applications, and transactions, marking a significant shift from traditional security models. It is not a one-time solution but requires a long-term commitment to adapting and evolving in response to innovative adversaries, emphasizing the need for ongoing vigilance and adaptability.
The Newest Attack Vectors — Infrastructure as Code & API Security
On-Demand — Moving applications and development to the cloud has delivered both operational and security benefits at scale. However, as organizations begin to automate their infrastructure deployments and configurations using Infrastructure as Code (IaC), a new attack vector has been introduced. In addition, the move to cloud-native architectures increases the use of APIs connecting client applications to cloud hosted, microservices based solutions, introducing another new entry point for adversaries.
A panel of industry experts and Government leadership discusses the security implications with IaC and APIs, and provides recommendations for addressing these new attack vectors.
DevSecOps: Analyzing Legacy Apps for Agile Development
On-Demand — The transition to Agile development is complex and challenging, especially for legacy programs. Where do you start and what obstacles may exist? Agile and DevSecOps are often touted as silver bullets to accelerating delivery of mission winning capability. These modern development and deployment methodologies offer many benefits, but navigating their implementation requires a data-driven understanding of which applications will benefit the most, and which impediments need to be addressed first.
Our panelists — with deep experience in government — will discuss how they have navigated and implemented Agile transformation programs in their organizations. They will highlight approaches to assessing program readiness, anticipating, and removing obstacles, and ongoing monitoring and measurement of continuous agile improvement.
DevSecOps Public Sector Accelerated ATO Initiative
On-Demand — Discussion on how Government agencies take advantage of rapid development/deployment techniques, such as DevSecOps, while meeting their ATO and security requirements in the same timely fashion.
Interactive Security Testing, DevSecOps, and NIST SP 800-53 Rev. 5
On-Demand — Discussion with top industry leaders including Dr. Ross from NIST, to highlight the latest security guidance under NIST SP 800-53, Rev. 5, and the role security plays as organizations migrate applications to the Cloud and embrace DevSecOps.
A Better Approach for Agencies to Put Security in DevOps
On-Demand — Learn why AST solutions must be capable of being completely automated within the tooling that is already in use within DevOps, how to ensure vulnerabilities in custom code, open-source, and run-time risks are identified and remediated early in an automated fashion, and explore the benefits of integrating automation into DevOps, resulting in improved quality, accuracy, security, and speed of delivered software.
An AppSec Awareness Program for Developers: The Critical Steps to Success
On-Demand — This webinar will explain the kinds of ad-hoc programs that exist in many agencies today; provide details of what a modern Awareness Program looks like; discuss the four key areas that must be addressed before starting; highlight the best way to organize your approach and setup; emphasize how to kickstart and launch your Awareness Program; and clarify the assessment process and ways to continuously improve
How to Address Security Vulnerabilities in the Development Lifecycle
On-Demand — Learn how your public sector agency can reduce the time and effort needed to incorporate security into the development process - and in the process avoid having to do costly remediation after the fact. This course was created in partnership with Checkmarx and DLT Solutions.
Speakers
Tim Anderson — Tim Anderson is a Sr. Security Advisor with AWS Security where he focuses on addressing the security, compliance, and privacy needs of customers and industry globally. He regularly meets with security leaders to advocate for rational, outcome-focused security that harnesses innovation. Additionally, Tim designs solutions, capabilities, and practices to teach and democratize security concepts such as security governance at scale and DevSecOps to meet challenges across the global landscape. Previous to AWS, Tim spent 16 years designing, delivering, and managing security and compliance programs for U.S. Federal customers across DoD and federal civilian agencies.

Parham Eftekhari — Parham Eftekhari served as ICIT’s Founder & Executive Director until April 2020 and now serves as Chairman of the Board. During his time as Executive Director, he was responsible for building and executing the Institute’s mission, including its content and education strategy, community engagement, and fundraising. Currently, Parham is SVP of the Cyber Risk Alliance and Executive Director of its Cybersecurity Collaborative business, a membership community defined by CISO collaboration offering strategic and tactical guidance, CISO career development, and industry advocacy. Prior to ICIT, Parham co-founded the IT collaboration group GTRA and led the technology practice at a boutique competitive intelligence research firm.

Stephen Gates — Stephen Gates brings more than 15 years of information security experience to his role at Checkmarx. He has an extensive hands-on background in the deployment and implementation of on-premises and cloud-based security solutions and is a well-known writer, blogger, presenter, and published author with a Master of Science in Information Security. Stephen is dedicated to conveying facts, figures, and information that brings awareness to the cybersecurity issues all organizations face. Aligning with Checkmarx's mission of improving software security for all organizations, he is an advocate of their solutions worldwide.

Jeff Hsaio — Jeff Hsiao is Security Solutions Engineer for Checkmarx Inc. Jeff is an experienced Information Technology professional with a background in Application Security, Software Development, and Program Management. Prior to his current role, Jeff served as a Technical Architect for large government programs. Jeff has designed and implemented technical solutions for dozens of Federal agencies and Fortune 500 companies across multiple industries.

James Hofsiss — James Hofsiss is a U.S. Air Force veteran with more than 30 years’ experience in cybersecurity and IT operations & management. As a DLT Sales Engineer, he is a trusted advisor, leveraging his broad expertise to support government customers at the federal state, and local levels.

Joyce Hunter — Joyce Hunter is a strategic-doer and a philantropreneur, Joyce is the CEO of Vulcan Enterprises LLC, a strategic management consulting organization, providing executive coaching and Information Technology advisory services to corporate, federal, and non-profit CXO’s. She is the creator of the Science Technology Engineering Agriculture and Math (STEAM) summer camp for underserved/underrepresented youth and has recently been named as the new Executive Director of the Institute for Critical Infrastructure Technology (ICIT). Joyce is also the former Acting Chief Information Officer for Policy and Planning at the Department of Agriculture.

Kurt Risley — Kurt Risley is the Global SME for Checkmarx's Codebashing Platform and a frequent speaker at industry events. Kurt brings many years of Cyber Security experience and has been in the Enterprise Software space for 20+ years. Codebashing is Checkmarx's Application Security Awareness Platform.

Matt Rose — Matt Rose, Global Director of Application Security Strategy, joined Checkmarx in 2014 and has over two decades of software development, sales engineering management, and consulting experience. In his role, he advises organizations' software security and DevOps strategies and enables them to deploy Checkmarx's solutions to protect their most critical application and software assets. Matt has been invited to deliver talks at leading industry events including OWASP's AppSec USA, IDG's CSO50 Conference, ISSA, and ISACA, and has been quoted in numerous news outlets such as TechTarget's SearchSecurity, Dark Reading, and TechRepublic.

Ron Ross — Ron Ross is a Fellow at the National Institute of Standards and Technology. His focus areas include computer security, systems security engineering, and risk management. Dr. Ross leads the Federal Information Security Modernization Act (FISMA) Implementation Project and Systems Security Engineering Project, which includes the development of security and privacy standards and guidelines for the federal government, contractors, and United States critical infrastructure. He also leads the Joint Task Force, an interagency group that includes the Department of Defense, Office of the Director National Intelligence, U.S. Intelligence Community, and the Committee on National Security Systems, with responsibility for developing a Unified Information Security Framework for the federal government and its contractors.
Dr. Ross has authored or coauthored many publications on risk management, cybersecurity, systems security engineering, and cyber resiliency. His publications include Federal Information Processing Standards 199 (security categorization) and 200 (security requirements); and Special Publications 800-30 (risk assessments), 800-37 (Risk Management Framework), 800-39 (enterprise risk management), 800-53 (security and privacy controls), 800-53A (security control assessments), 800-160, Volume 1 (systems security engineering), 800-160, Volume 2 (cyber resiliency), 800-171 (protection of Controlled Unclassified Information in nonfederal systems and organizations), 800-172 (enhanced security requirements for advanced cyber-threats) and 800-171A (security assessments for nonfederal systems and organizations).

Nick Sinai — Nick Sinai is a Senior Advisor at Insight Partners, a leading global venture capital and private equity firm investing in high-growth software companies. Founded in 1995, Insight Partners has raised more than $29 billion and invested in more than 300 growth-stage software and internet companies. Nick joined Insight in 2014 from the White House, where he was U.S. Deputy Chief Technology Officer. At the White House, Nick led President Obama’s Open Data Initiatives, co-authored President Obama’s 2013 Executive Order making open and machine-readable the default for new government information, led the relaunch of Data.gov and was a national advocate for open government data. Nick also helped start and grow the Presidential Innovation Fellows program, which brings entrepreneurs, innovators, and technologists into government. In January 2017, in his very last act in office, President Obama signed bipartisan legislation that makes the Presidential Innovation Fellows Program a permanent part of the Federal government going forward. Nick serves as adjunct faculty at the Harvard Kennedy School, where he teaches technology and innovation in government field class. Nick is also an advisor to Upsolve, a Brooklyn-based nonprofit that improves consumer access to Chapter 7 bankruptcy protection, and Coding It Forward, a nonprofit that places computer science, data science, and design students in federal agencies.

Rick Stewart — Rick Stewart is a Chief Software Technologist at DLT, a Tech Data Company. Rick has more than 34 years of diverse experience in the IT industry, progressing through technical and leadership roles in the telecommunications, mobile entertainment, the federal government, and manufacturing industries. His primary area of expertise is in developing enterprise application software, and he's proficient in a wide range of software technologies. He has vast experience managing project teams of various sizes and skillsets using both waterfall and agile/Scrum software, DevOps, and DevSecOps development methodologies. He has participated in all phases of the software development life cycle and supported highly available production environments and is Project Management Professional (PMP) and Agile Certified Professional (ACP) certified.

- National Cybersecurity Strategy – GAME ON!
- What the New NIST Guidance Means for Embedding Security into DevOps
- Why AppSec Training is Essential for Government Agencies Today
- How the Air Force and SSA Navigate the (Sometimes Bumpy) Road to DevSecOps
- How DevSecOps and Automation Can Accelerate ATOs
- The Challenges of Open Source Software and How to Solve Them
- Five Reasons to Prioritize AppSec in Your Agency
- Four Ways to Combat Developer Burnout
- Four Best Practices for Securing Cloud-Native Applications
- Move it left, all the way left – Application Security as strategy creates advantages
- From "Trust but Verify" to "Never Trust" – the Importance of AST in application development