As local and state government officials prepare for the 2020 general election, many are still looking for unique election security solutions to protect voters. DLT Solutions and our election security partners understand the urgent need to deliver solutions designed to strengthen the U.S. Government security needs.
Check out DLT's election security exclusive hub equipped with podcasts, blogs, information on unique solutions, and so much more!
DLT's Election Security Podcasts!
As part of raising awareness about election security and the issues that U.S. government officials face, DLT is hosting four specialized podcast episodes with insightful guest speakers! These exclusive podcast episodes will present different perspectives on critical election infrastructure issues facing state and local governments.
Discover More on Transformational Election Security Solutions
AWS
Elections face an array of sophisticated threats designed to undermine system integrity and public trust. With AWS, election administrators and political campaigns are empowered to focus on the core needs of the electorate in a secure, scalable, and cost-effective way rather than building and maintaining the underlying infrastructure to support mission-critical efforts. Over 6,500 government agencies around the world use AWS. In states and counties across the US, elections infrastructure and workloads of varying scope and scale rely on the services and support of AWS and its partner network. Learn how AWS can help — Contact us!
Cherwell
Cherwell empowers State & Local agencies to transform their business through the rapid adoption and easy management of digital services. Cherwell’s adaptable platform has enabled thousands of agencies to modernize their business operations with customizable service management, automation, and reporting across the enterprise. Learn how Cherwell can help — Contact us!
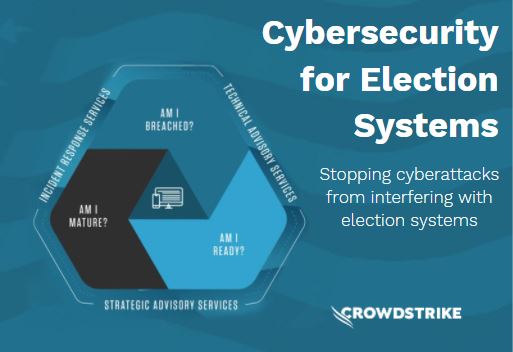
CrowdStrike
We Stop. So you can go. State election committees and IT leaders need to protect the integrity of the voting process by preventing unauthorized access to the election systems. CrowdStrike’s advisory services provide the best practice frameworks needed to assess and enhance cyber maturity levels across the voting process, leveraging deep cybersecurity expertise and the global threat intelligence from the CrowdStrike Falcon Platform and Falcon OverWatch threat hunting team. Learn how CrowdStrike can help — Contact us!
Red Hat
Red Hat understands the importance of protecting democracy by providing the public sector with trusted election security technologies. Red Hat IT security preserves the integrity of information technologies like computer systems, networks, and data from attack, damage, or unauthorized access. As state and local agencies continue to prepare for our primary elections, it’s critical to understand how to adopt security solutions that begin with design. This is what it means to "shift security left" — to make security a part of the infrastructure and product lifecycle as early as possible. This helps security be both proactive and reactive. Our mission is to help protect customers from meaningful security concerns when using Red Hat products and services. There is no better time than now to enhance your knowledge on Red Hat secure products and services — Technology build for change. Learn how Red Hat can help — Contact us!
Election Security Resources
DLT Solutions believes in sharing valuable resources such as blogs, white papers, and eBooks in order to bring to light election security solutions. Check out DLT's newest blogs on election security issues and how partners can solve them!
Recently Adam Meyers, SVP of Intelligence at CrowdStrike, and a DLT partner, hosted a webinar called "Protecting Our Nation's Election Infrastructure in 2020". In this webinar, Adam provides insight into the motivations behind attacks launched by threat actors who are targeting government agencies and private companies. Furthermore, during this webinar, Adam explains how CrowdStrike tracks threat actors from different countries by code names and how CrowdStrike Intelligence tracks sophisticated (techniques tactics and procedures (TTPs).
Government officials, particularly at the local level, not only have to contend with a pandemic but also an increase in digital threats such as ransomware attacks. These attacks are being used to create chaos in political campaigns and steal voting data before election day. Specifically, ransomware attacks can create confusion on election day and cause irreversible damage, such as deleting voter registration databases, voting tabulation, or stealing sensitive records containing personal information. The question that needs to be asked is, how can local and state government authorities combat the threat of these ransomware attacks?
Election security is a big topic, but it resembles a many-legged centipede. Federal contractors face the reality that elections are the purview of state, county and municipal officials. The technical and managerial abilities of these entities vary from what you might expect in a tiny hamlet to what you might encounter in a million-person suburban county. Not to push the analogy, but the mail-in Census option resembles the mail-in balloting process that’s expanded so much in recent years. Both electronic and mail balloting are likely to balloon as the coronavirus threat affects nearly every governmental process.
Cybersecurity is a fundamental pillar of election security. The elections community–and their partners in government, NGOs, and the private sector–must remain vigilant in the face of potential threats. Elections infrastructure and systems, enterprises that administer elections, campaigns, and the channels through which elections information and results are communicated, can all be targeted. Learn how CrowdStrike can help.
Federal and State officials, including the FBI, have explained that it would be difficult for any bad actor to coordinate any fraud scheme involving mail ballots. This is due to the numerous safeguards in place designed to protect U.S. elections. Furthermore, experts point out that the concern is not technology, but if the board election will have the massive workforce needed to verify each returned ballot. So many election officials are now relying on signature-verification software that some security specialists fear hackers could exploit this technology.
Valuable Resources
- Protecting Our Nation’s Election Infrastructure in 2020
- Scaling to Share Unprecedented Volume of Election Donation Data, Quickly and Cost-effectively
- Harvard Belfer Center: Cybersecurity Playbooks
- Election Assistance Commission: Election Security Resources
- National Association of Secretaries of State: Trusted Info 2020 Campaign
- Global Cyber Alliance: Elections Toolkit
- Department of Homeland Security (DHS): Election Security Resources
- DHS: Election Security Strategic Plan
- DHS: CISA Cyber Essentials
- DHS: CISA Central