A Closer Look at Blockchain and Supply Chain Risk Management
“Build it in, don’t bolt it on” is a mantra we all learn when we study cybersecurity, yet we see it in practice far too rarely. Our adversaries also know this principle and have begun to implement it by infecting the supply chain – hardware and software – as close to the source as possible. DLT technology partners Crowdstrike and Symantec both note the trend in recent threat reports. In their July,2018 report1, Crowdstrike notes that:
• Two-thirds of respondents reported had experienced a software supply -chain attack
• 90% of the survey respondents believe they are at risk for a supply chain attack
• Organizations are still slow to detect, remediate and respond to threats, and yet only one-third of respondents vet all of their suppliers
Symantec’s 2018 report2 agrees:
• “Symantec is now seeing an increase in attackers injecting malware implants into the supply chain to infiltrate unsuspecting organizations, with a 200 percent increase in these attacks—one every month of 2017 as compared to four attacks annually in years prior
• Hijacking software updates provides attackers with an entry point for compromising well-protected targets, or to target a specific region or sector”2
Some specific examples come to mind. In 2017, attackers compromised the development environment of a PC tool called CCleaner, infected the software, and unwitting users downloaded updates – validated by the company’s certificate – to their machines. Other attackers took much the same approach with the Petya/NotPetya attack. A more sophisticated approach emerged when bad actors compromised BGP routing tables and re-routed update traffic through Russia, where updates were poisoned.
Why are attackers taking this approach? Again, Symantec and Crowdstrike agree: creating zero-day attacks has become more difficult, so our adversaries are taking a different approach. Moreover, that approach makes it easier to hide, and provides a bigger “bang for the buck”; by compromising one company, they can infect a large number of machines. According to Avast, 2.27 million users downloaded the infected version of CCleaner.3
In October, Bloomberg announced that China had infected servers in the United States were by altering CPU chips. This announcement is controversial, but what matters is that it could have happened: there is no real way to know if this happened or could happen again. Quite simply, we are not in control of the supply chain, for hardware or software.
We need to address the problem from two angles: human behavior, and technology. For recommendations on the human behavior side, look to an excellent document Mitre created, called “Deliver Uncompromised” (DU). DU offers 15 separate courses of action (COAs), many of which recommend financial or economic incentives. The first recommendation, for instance, is for DoD to give preferential treatment to contractors and vendors who can demonstrate that their software or hardware is truly secure. The document also advocates tax breaks for companies investing heavily in cybersecurity and generally recommends that security become the “fourth pillar” of product and service evaluation, equal in importance to schedule, cost, and performance.
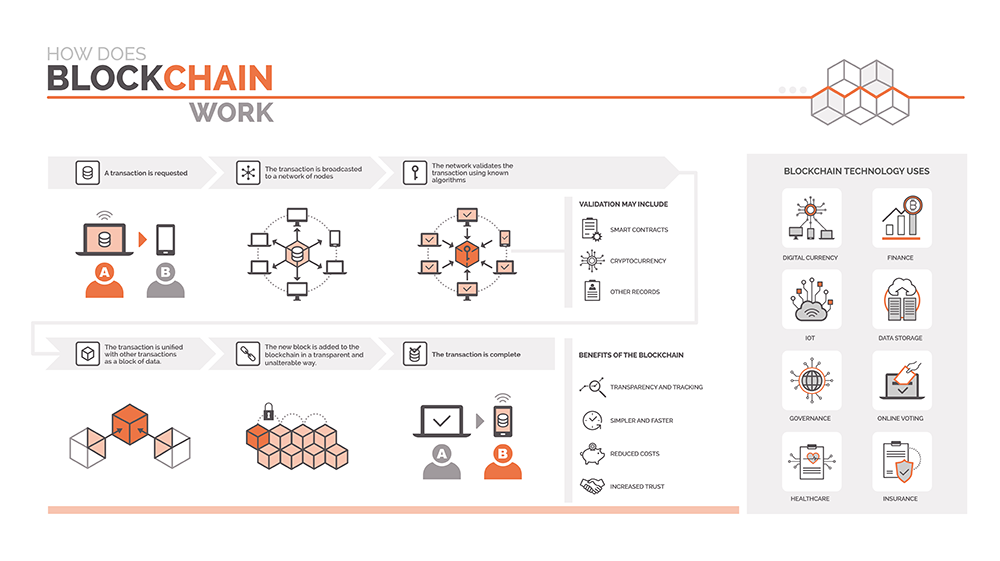
These are worthy aims, but making them real requires technology, and blockchain methods are worth a look. As I write this, there are several companies offering supply-chain management services using the immutable ledgers blockchain enables. The technology is viable in the real world, but unfortunately, many of those companies are based in China; we clearly need to catch up.
NIST, however, is doing their part. In February 2019, they published the snappily-titled document, “Securing the Digital Threat for Smart Manufacturing: A Reference Model for Blockchain-Based Product Data Traceability 4.”
Pulling apart the title and digging into the document reveals a cogent description of how blockchain-based technology can:
• Ensure that data sent is data received
• Track the provenance (sequence of ownership) of a piece of equipment (or software)
• Validate that all transactions involving the item are complete and satisfactory to all parties
Supply Chain Risk Management is a big topic and a big problem. Solutions must involve incentives to encourage desired human behavior, and appropriate technology to facilitate and ensure data integrity, proof of provenance, and validity of transactions.
[1] Larson, D. (2018, July 23). Global Survey Reveals Supply Chain as a Rising and Critical New Threat Vector. Retrieved February 15, 2019, from Global Survey Reveals Supply Chain as a Rising and Critical New Threat Vector from https://www.crowdstrike.com/blog/global-survey-reveals-supply-chain-as-a-rising-and-critical-new-threat-vector/
[2] Cleary, G., & Et, Al. (2018). Internet Security Threat Report (Vol. 23, ISTR, p. 5). Mountain View, CA: Symantec.
[3] Steckler, V., & Vlcek, O. (n.d.). Progress on CCleaner Investigation. Retrieved February 15, 2019, from https://blog.avast.com/progress-on-ccleaner-investigation
[4] Krima, S., Hedberg, T., & Feeney, A. B. (2019, February). Securing the Digital Threat for Smart Manufacturing: A Reference Model for Blockchain-Based Product Data Traceability. Retrieved February 15, 2019, from https://nvlpubs.nist.gov/nistpubs/ams/NIST.AMS.300-6.pdf

















































