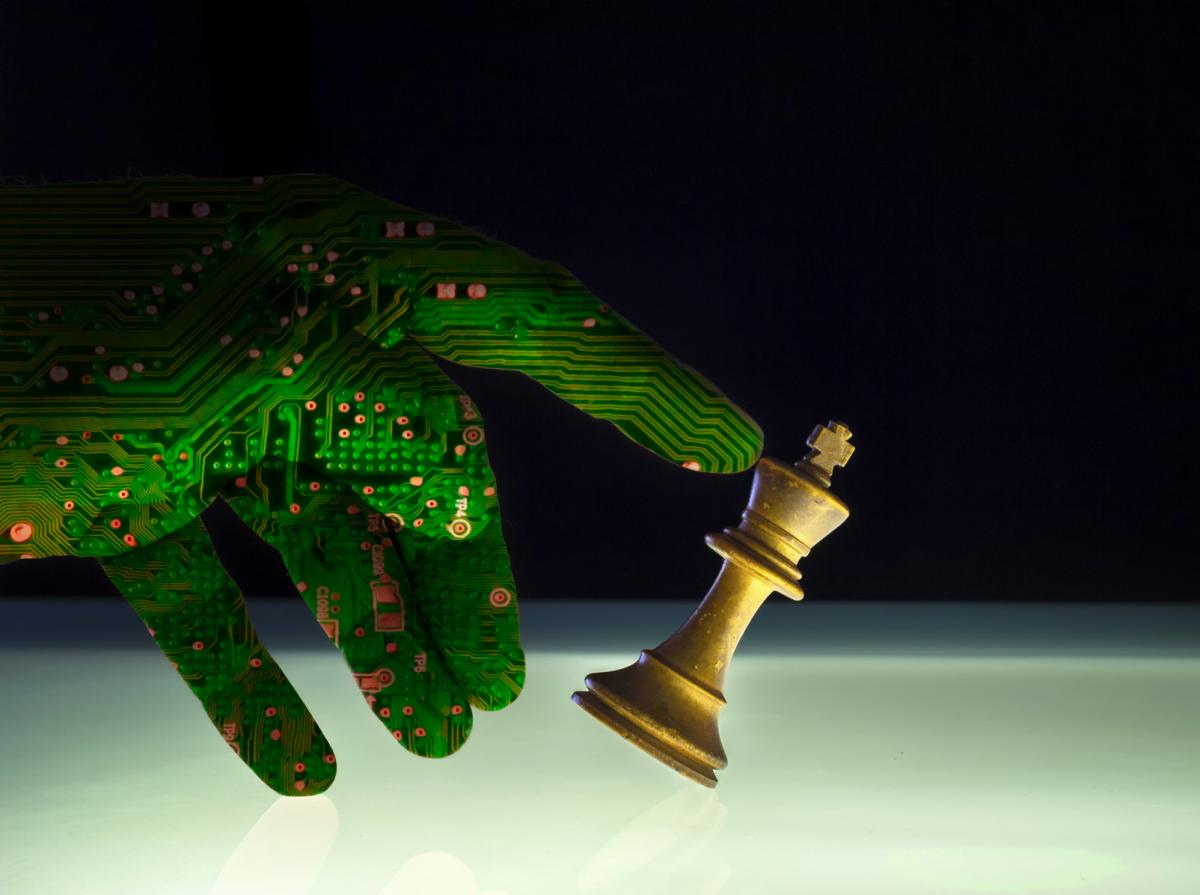
The 2017 DefCon conference featured former World Chess Champion Garry Kasparov, who spoke about artificial intelligence, computers, and of course, chess. After losing a match to a purpose-built computer in 1997, Kasparov realized that the machine, although it had beaten him, was not truly intelligent: it had simply out-calculated him, by examining over 200 million chess positions per second. Kasparov soon devised “advanced chess”, in which a strong human player teams up with a computer. Advanced chess combines the best human qualities of imagination, judgment, and capacity for abstract concepts, with the power and calculation accuracy of computers. The result is the strongest chess currently possible.
Top flight threat-hunting tools leverage this human-computer teamwork in a much more dangerous game: cybersecurity. A chess player faces a bewildering array of possibilities – mathematicians estimate of the number of possible chess games at well over the number of atoms in the universe – and uses logic, intuition, and a bit of calculation to try to win. Security analysts also face a tsunami of possibilities derived from logs, alerts, more logs, threat intelligence, and more, from which they must perceive and remediate threats. Some say it’s like finding a needle in a haystack; security insiders compare it to finding a specific needle in a stack of nearly identical needles.
Clearly, humans cannot process so much information, so an automated threat-hunting tool is essential. Human curiosity, intuition, and judgment are still indispensable. To find and stop threats, we need to follow Kasparov’s lead, and amplify the best human qualities with the power, speed and accuracy of a computer. Just as Kasparov created “advanced chess”; we need “advanced threat hunting”.
A chess game is a fair fight: all the pieces are plainly visible, and both players have the same army. Cybersecurity is not so equitable. Defenders have a small, often inexperienced staff, while attackers are vast in number, and often include highly talented actors. Even worse, they can attack surreptitiously: your data can be stolen, and you might not even know.
Therefore, it is essential to assume attackers have breached your systems, hunt for the threats, and make sure they are mitigated. You need a top quality threat-hunting tool, but what qualities feature prominently in an effective system?
First, it must be able to ingest data from just about anywhere – alerts, application logs, system logs, device logs, identity management systems, threat intelligence data, full packet capture from network devices, and so on. Data ingestion doesn’t mean much, though, unless the system can identify patterns, and present them to humans in an intuitive, graphical interface.
Most importantly, a threat-hunting tool must be a good partner to humans, by letting people form hypotheses about possible threats, and then searching for such threats as quickly and intuitively as possible. The people hunting for threats must have some knowledge of cybersecurity, but the threat hunting system should amplify that knowledge, to facilitate the real goal of fixing the problem as quickly as possible.
DLT partners with Sqrrl, a leading threat hunting tool that finds threats quickly, and leverages skills and knowledge of overburdened security teams. Sqrrl lets organizations deploy “advanced chess” – humans and computers working together – on the very real and dangerous battlefield of cyberspace.
To register for an upcoming webinar on Data Staging and Exfiltration, click here: http://info.sqrrl.com/hunting-for-data-staging-and-exfiltration
For a practical guide to threat hunting, click here: http://info.sqrrl.com/practical-threat-hunting

















































