Fed IT Security Hardens, but User Authentication Remains Weak
On February 27, FISMA presented its annual report to Congress. The report (compiled by the OMB) provides metrics on federal cybersecurity incidents, efforts to mitigate them, and progress in implementing cybersecurity policies and programs.
The good news is that there is progress to report, with nearly 70,000 information security issues reported in FY’ 2014, up 15% over the previous year – there is still work to be done.
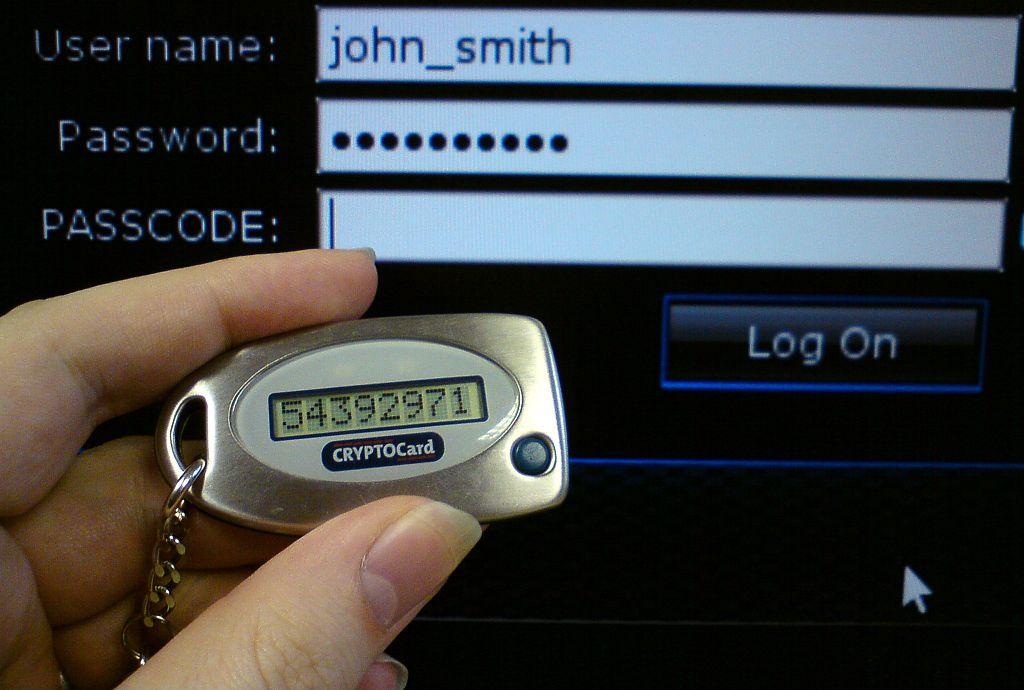
The biggest concern remains in the area of authentication (aka “knowing your users”). While the DoD is doing a good job of “strong authentication”, strip those numbers from the report and only 41% of civilian CFO Act agencies implemented use of strong authentication for network access last fiscal year.
“Strong authentication” requires that an increasing number of agencies require their users to log-on to networks with unique Personal Identity Verification (PIV) cards, instead of other less secure means of identification and authentication.
An analysis of cyber threats and high-profile data breaches found that “the majority of federal cybersecurity incidents are related to or could potentially have been mitigated by Strong Authentication implementation.”
Incidents that “could have been allayed by the implementation of Strong Authentication” were identified as:
- Improper Usage, Suspicious Network Activity, and Unauthorized Access – Improper user behavior can be deterred by reducing anonymity through Strong Authentication.
- Social Engineering, Phishing, and Malicious Code – These incident types can be deterred through use of PIV card capabilities like digitally signing emails, and delivering corresponding user training to thwart phishing attempts.
- Denial of Service, Equipment, and Other – These incident types are not typically related to Strong Authentication implementation.
- Non-Cyber – This incident type was removed from the analysis since it is not related to cybersecurity incidents.
Learn more about managing authentication for files, applications, and networks.
Featured image by Brian Ronald (Photographed by uploader) [GFDL (http://www.gnu.org/copyleft/fdl.html) or CC BY-SA 4.0-3.0-2.5-2.0-1.0 (http://creativecommons.org/licenses/by-sa/4.0-3.0-2.5-2.0-1.0)], via Wikimedia Commons

















































