Technically News scans thousands of industry articles to present you with a weekly source of IT news, information, and ideas that impact the public sector.
While the private sector is innovating, seemingly, at the speed of Moore’s law, the public sector is still grabbling with the concepts and adjusting itself to the flexibility needed in order to embrace new emerging technologies. Steve Towns, executive editor of Governing, argues that the slow IT procurement process is one of the lesser-discussed roadblocks to “government 2.0.”
Saving Government Tweets is Tougher Than You Think
There are two kinds of big data in government: the kind collected to analyze and improve services and the kind, it seems, merely collected. The National Archive and Records Administration has drafted guidance for the later in a document subjected Guidance on Managing Social Media Records. NextGov puts context to the problem in Saving Government Tweets is Tougher than You Think.
Enterprise Cybersecurity: The Case for Using Analytics to Manage Risk
It’s not a question of “if” your agency is going to be cyberattacked, it’s when. And for cybersecurity officials, the bigger question is will the hacker succeed? Chris Smith, Director of enterprise architecture and service engagement for SAS Federal, has written an editorial arguing that using analytics to manage risk will help IT managers sleep better at night.
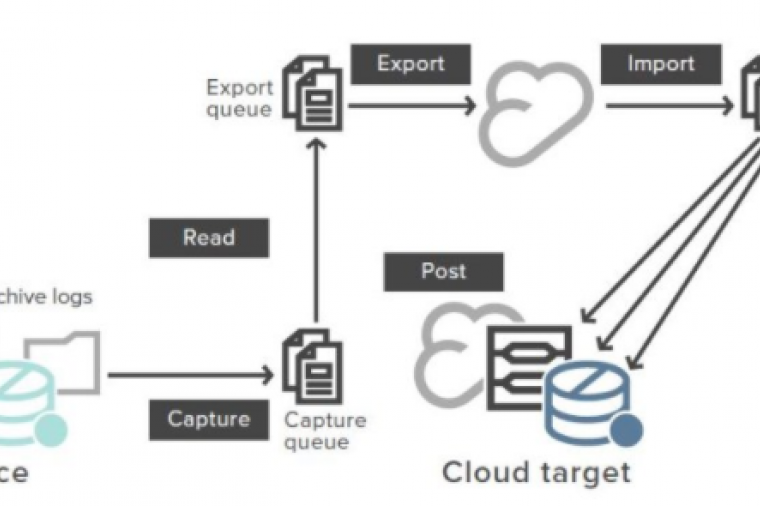
Defense Dept. Seeks $450M Cloud Builder
Calling all clouds: the contracting office of the Defense Information Systems Agency (DISA) wants to build a cloud for the U.S. Defense Department valued at $450 million. It hasn’t been publicly established if this is for a private, public, or hybrid solution. This isn’t the first massive cloud procurement opportunity from the government. The CIA recently awarded Amazon Web Services a $600 million contract for their private cloud solution. InformationWeek has the DISA summary.
What’s Wrong with Cybersecurity Training?
As the government increases cybersecurity training to defend our nation’s networks, FCW asks if they’re going about it the wrong way. The writer, Amber Corrin, points out that while they’re doing a great job training the theoretical elements, officials are not doing a good enough job of preparing students for the real world aspects. I’ll also add that while training tech-focused “cybersecurity warriors” is important, almost as important is ensuring that anyone with access to agency networks understand the basics of online security. Read the article to see if you agree with Amber’s assertions.
Five Steps to Make FedRAMP Work for You – According to DLT’s Chief Cloud Technologist
Last week, our Chief Cloud Technologist, David Blankenhorn, wrote “Five Steps to Make FedRAMP Work for You” for Washington Technology. While many agencies are excited to move assets to the cloud, the granularity of FedRAMP has caused delays. David has written a guide for CSPs about to go through the process.